A Network Security Model exhibits how the security service has been designed over the network to prevent the opponent from causing a threat to the confidentiality or authenticity of the information that is being transmitted through the network.
In this section, we will be discussing the general ‘network security model’ where we will study how messages are shared between the sender and receiver securely over the network. And we will also discuss the ‘network access security model’ which is designed to secure your system from unwanted access through the network
For a message to be sent or receive there must be a sender and a receiver. Both the sender and receiver must also be mutually agreeing to the sharing of the message. Now, the transmission of a message from sender to receiver needs a medium i.e. Information channel which is an Internet service.
A logical route is defined through the network (Internet), from sender to the receiver and using the communication protocols both the sender and the receiver established communication.
Well, we are concerned about the security of the message over the network when the message has some confidential or authentic information which has a threat from an opponent present at the information channel. Any security service would have the three components discussed below:
1. Transformation of the information which has to be sent to the receiver. So, that any opponent present at the information channel is unable to read the message. This indicates the encryption of the message.
It also includes the addition of code during the transformation of the information which will be used in verifying the identity of the authentic receiver.
2. Sharing of the secret information between sender and receiver of which the opponent must not any clue. Yes, we are talking of the encryption key which is used during the encryption of the message at the sender’s end and also during the decryption of message at receiver’s end.
3. There must be a trusted third party which should take the responsibility of distributing the secret information (key) to both the communicating parties and also prevent it from any opponent.
Now we will study a general network security model with the help of the figure given below:
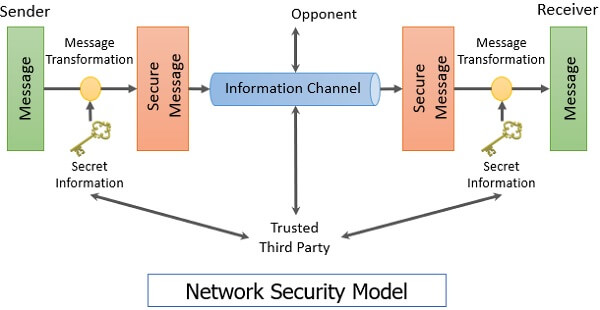
The network security model presents the two communicating parties sender and receiver who mutually agrees to exchange the information. The sender has information to share with the receiver.
But sender cannot send the message on the information cannel in the readable form as it will have a threat of being attacked by the opponent. So, before sending the message through the information channel, it should be transformed into an unreadable format.
Secret information is used while transforming the message which will also be required when the message will be retransformed at the recipient side. That’s why a trusted third party is required which would take the responsibility of distributing this secret information to both the parties involved in communication.
So, considering this general model of network security, one must consider the following four tasks while designing the security model.
1. To transform a readable message at the sender side into an unreadable format, an appropriate algorithm should be designed such that it should be difficult for an opponent to crack that security algorithm.
2. Next, the network security model designer is concerned about the generation of the secret information which is known as a key.
This secret information is used in conjunction with the security algorithm in order to transform the message.
3. Now, the secret information is required at both the ends, sender’s end and receiver’s end. At sender’s end, it is used to encrypt or transform the message into unreadable form and at the receiver’s end, it is used to decrypt or retransform the message into readable form.
So, there must be a trusted third party which will distribute the secret information to both sender and receiver. While designing the network security model designer must also concentrate on developing the methods to distribute the key to the sender and receiver.
An appropriate methodology must be used to deliver the secret information to the communicating parties without the interference of the opponent.
It is also taken care that the communication protocols that are used by the communicating parties should be supporting the security algorithm and the secret key in order to achieve the security service.
Till now we have discussed the security of the information or message over the network. Now, we will discuss the network access security model which is designed to secure the information system which can be accessed by the attacker through the network.
You are well aware of the attackers who attack your system that is accessible through the internet. These attackers fall into two categories:
1. Hacker: The one who is only interested in penetrating into your system. They do not cause any harm to your system they only get satisfied by getting access to your system.
2. Intruders: These attackers intend to do damage to your system or try to obtain the information from the system which can be used to attain financial gain.
The attacker can place a logical program on your system through the network which can affect the software on your system. This leads to two kinds of risks:
a. Information threat: This kind of threats modifies data on the user’s behalf to which actually user should not access. Like enabling some crucial permission in the system.
b. Service threat: This kind of threat disables the user from accessing data on the system.
Well, these kinds of threats can be introduced by launching worms and viruses and may more like this on your system. Attack with worms and viruses are the software attack that can be introduced to your system through the internet.
The network security model to secure your system is shown in the figure below:
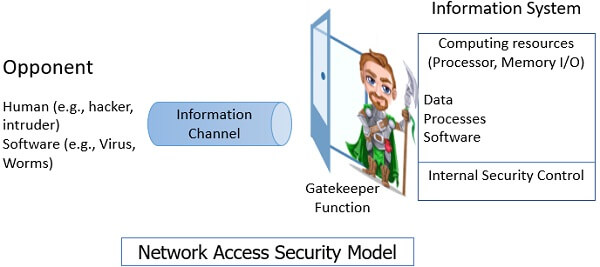
There are two ways to secure your system from attacker of which the first is to introduce the gatekeeper function. Introducing gatekeeper function means introducing login-id and passwords which would keep away the unwanted access.
In case the unwanted user gets access to the system the second way to secure your system is introducing internal control which would detect the unwanted user trying to access the system by analyzing system activities. This second method we call as antivirus which we install on our system to prevent the unwanted user from accessing your computer system through the internet.
So, this is all about the network security model. We have discussed two network security model. One, securing your information over the network during information transmission. Second, securing your information system which can be accessed by the hacker through the network or internet.

Harsh kumar says
Very nice when I was learning by book i can not understand the concept of network security but I read your article I can understand the concept of network security and also understand the network access security model
Neha says
Really, nice content and include additional information of the computer network security..
KIPROTICH PHILIP says
I am so pleased with your notes, I like the simple English used and very well explained, I have also been able to understand what has been confusing me alot