Public Key Cryptography is a cryptographic technique that involves ‘two distinct keys’ for encryption and decryption. That’s why it is also known as asymmetric-key cryptography. The public key cryptography is totally based on the ‘invertible mathematical’ function which makes it different from the conventional symmetric key cryptography.
It is not that symmetric key cryptosystem is less efficient than public key or the public key cryptosystem is superior. The security of any cryptosystem depends only the length of key and computation required in cracking the encrypted cipher text. In this section, we will be discussing the public key cryptography in brief along with its requirement, application and cryptanalysis.
Contents: Public Key Cryptography
- Principles of Public Key Cryptosystem
- Public Key Cryptography Requirements
- Public Key Cryptosystem Applications
- Public Key Cryptanalysis
- Key Takeaways
Principles of Public Key Cryptosystem
There are two basic principles of any cryptosystem i.e. confidentiality and authenticity. We have seen that the symmetric cryptosystem has a problem associated with these two principles.
In symmetric cryptography, the problem associated with confidentiality is that we all know in symmetric cryptography a secret key is used to encrypt as well as decrypt the message. So, this key must be shared by both the communicating parties by any means or they must rely on a third party for the distribution of the key i.e. key distribution centre. But relying on a third party again risk the secrecy of the secret key.
Symmetric key also had an issue with authentication. To become widespread there was a need for digital signatures that assure all parties that a particular message has been sent from a particular person.
The public key cryptosystem is successful in achieving both these principles i.e. confidentiality and authenticity. Let us discuss how?
We begin with first, encrypting the message using the senders private key. Now, as the message is encrypted using the sender’s private key it is confirmed that the message has been prepared by the sender. This does the function of the digital signature.
E(PRS, M)
Nobody is able o modify the message without having the sender’s private key. So, public key cryptosystem has achieved authentication in both the terms data integrity and source.
Now, the message that was first encrypted with the sender’s private key is again encrypted using the intended receiver’s public key.
M’ = E(PUR ,E(PRS, M)
The final cipher text can only be decrypted by the intended receiver’s private key which is only known to him. In this way, the public key cryptography achieves confidentiality.
The decryption of the final cipher text is:
M = D(PUS, D(PRR, M’)
There is a drawback with this approach. We all know that the public key cryptosystem is based on mathematical function and has too much of computation which makes it complex. To achieve both confidentiality and authenticity the public key algorithm has to be applied four times.
Public key Cryptosystem
Any public key cryptographic algorithm has six elements as follow:
- Plain Text
This is a readable message which is given as input to the algorithm. In a public key algorithm, the plain text is encrypted in blocks. - Encryption Algorithm
The encryption algorithm is implemented on the plain text which performs several transformations on plain text. - Public and Private keys
These are the set of keys among which if one is used for encryption the other would be used for decryption. The transformation of plain text by encryption algorithm depends on the key chosen from the set to encrypt the plain text. - Cipher Text
This is the output of encryption algorithm. The generated cipher text totally depends on the key selected from the set of the public and private key. Both of these keys, one at a time with plain text would produce different cipher texts. - Decryption Algorithm
This would accept the output of the encryption algorithm i.e. the cipher text and will apply the related key to produce the original plain text.
Now let us discuss the steps in public key cryptography.
Step 1. Each user has to generate two keys one of which will be used for encryption and other for decryption of messages.
Step 2. Each user has a pair of keys, among which one has to be made public by each user. And the other has to be kept secret.
Step 3. If a user has to send a message to a particular receiver then the sender must encrypt the message using the intended receivers public key and then send the encrypted message to the receiver.
Step 4. On receiving the message, the receiver has to decrypt the message using his private key.
In public key cryptography, there is no need for key distribution as we have seen in symmetric key cryptography. As long as this private key is kept secret no one can interpret the message. In future, the user can change its private key and publish its related public key in order to replace the old public key.
Public Key Cryptography Requirements
To accomplish the public key cryptography there are following requirements as discussed below.
- The computation of the pair of keys i.e. private key and the public key must be easy.
- Knowing the encryption algorithm and public key of the intended receiver, computation of cipher text must be easy.
- For a receiver of the message, it should be computationally easy to decrypt the obtained cipher text using his private key.
- It is also required that any opponent in the network knowing the public key should be unable to determine its corresponding private key.
- Having the cipher text and public key an opponent should be unable to determine the original message.
- The two keys i.e. public and private key can be implemented in both orders
D[PU, E(PR, M)] = D[PR, E(PU, M)]
Public Key Cryptosystem Applications
In public key cryptography, every user has to generate a pair of keys among which one is kept secret known as a private key and other is made public hence called as a public key. Now, the decision of whether the sender’s private key or receiver’s pubic key will be used to encrypt the original message depends totally on application.
We can classify the applications of the public key cryptosystem as below:
a. Encryption/Decryption
If the purpose of an application is to encrypt and decrypt the message then the sender has to encrypt the message using the intended receivers public and the receiver can decrypt the message using his own private key.
b. Digital Signature
If the purpose of the application is to authenticate the user then the message is signed or encrypted using the senders private key. As only the sender can have its private key, it assures all parties that the message is sent by the particular person.
c. Key Exchange
The two communicating parties exchange a secret key (maybe a private key) for symmetric encryption to secure a particular transaction. This secret key is valid for a short period.
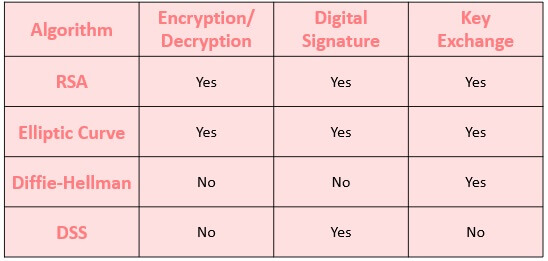
Well, some algorithms implement all the three application and some implement one or two among these applications. Below is the image showing you the details of algorithm possessing these applications.
Public Key Cryptanalysis
To prevent the brute force attack the key size must be kept large enough so that it would be impractical for an adversary to calculate the encryption and decryption. But the key size should not be so large such that it would become impractical to compute practical encryption and decryption.
Another type of attack in public key cryptography is that the adversary would try to compute private key knowing the public key.
One more type of attack is probable message attack. If an adversary knows that the encrypted message from a particular sender is a 56-bit key. Then he would simply encrypt all possible 56-bit keys using the sender’s public key as the public key is known to all. And then match all the encrypted messages with the cipher text. This type of attack can be prevented by appending some random bits to the original message.
Key Takeaways
- Public key cryptosystem is one which involves two separate keys for encryption and decryption.
- Each user participating in the communication has to generate two keys, one is to be kept secret (private key) and one is to make public (public key).
- Public key cryptosystem can achieve both confidentiality and authenticity.
- The public key cryptosystem is based on invertible mathematics so it has too much of computation.
- Large key size reduces the probability of brute force attack in public key cryptosystem
- Examples of public key cryptosystem are RSA, Diffie-Hellman, DSS and Elliptic curve.
So, this is all about the public key cryptosystem. Till now, we have studied applications, requirements, principles and cryptanalysis of public key cryptography.

Bilal khan says
This topic is very informative for me and in very easy wording …. Everyone can understand it easily in the pressure of exam ….. thanks for this informative topic
Sarthak says
I enjoy reading your site posts