Multiple access control is a method that allows multiple stations to share the same link. Well, the data link layer is responsible for the transmission of frames between the sender and receiver. We can classify the function of the data link layer into two types:
- Data Link Control
- Multiple Access Control
The data link control protocols offer reliable communication when there is a dedicated link between the communicating stations. If there is a dedicated link, the data link control protocols are self-sufficient to handle the framing, flow and error control.
What if multiple stations share the same link?
Then the multiple access control protocols resolve the access to the share link/channel/media. If multiple stations share the same link, then the multiple access control protocols help stations to identify which station currently has control over the link at any given time.
In this section, we will learn multiple access control protocols in detail. So, let’s start.
Content: Multiple Access Control
Content: Multiple Access Control
- What is Multiple Access Control
- Random Access Protocols
- Controlled Access Protocols
- Channelization Protocol
What is Multiple Access Control?
The data link layer is divided into two functionality-oriented sub-layers. The first sublayer, i.e. data link control layer, regulates the flow of frame between the nodes when there is a dedicated link between them. We also refer to the first sub-layer as logical link control (LLC)
The second sublayer, i.e. multiple access control (MAC), coordinates the access to the shared link. It is similar to the scenario of a classroom where multiple students try to answer their teacher simultaneously. In that case, it becomes the responsibility of the teacher to make the students speak one by one so that their answers make sense without creating chaos.
The same is the situation with multipoint networks. So, we require multiple access protocols to handle access to the shared link. Now, these protocols are divided into three categories where each category holds a group protocol, as you can see in the figure below: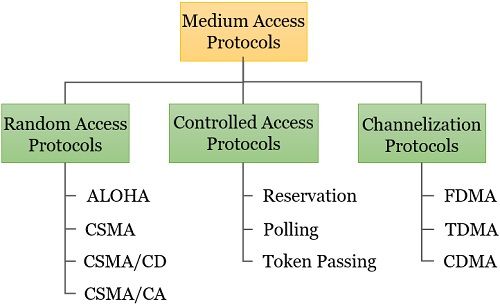
Random Access Protocol
In the random-access method, all the stations in a network have equal priority. The decision to send a frame on the link depends on its state, whether the link is busy or idle. So, a station can transmit a frame whenever it wants to but before checking the state of the link.
The random-access protocols have evolved from a very simple protocol known as ALOHA.
ALOHA
In the early 1970s, the University of Hawaii developed a protocol to regulate data transmission on wireless LAN known as ALOHA. Although the ALOHA protocol was also applicable to the shared link. The ALOHA protocol has two variations.
- Pure ALOHA
- Slotted ALOHA
Pure ALOHA
The original ALOHA protocol is referred to as pure ALOHA protocol. The strategy is that a station can transmit a frame whenever it wants to without checking the state of the link. So, there is a maximum chance of collisions as another station may attempt to transmit the frame at the same time.
When the frame from the two stations collides, it gets destroyed. The protocol relies on the acknowledgement from the receiver. So, when a station transmits a frame, it expects an acknowledgement for the same. And when it doesn’t receive the acknowledgement before the time-out period, it assumes that either the frame or the acknowledgement got destroyed, and it resends the frame again.
We know that collision occurs when two or multiple stations try to send a frame simultaneously. So even if the stations try to resend the frame after a fixed time-out, the frame from the stations will collide again.
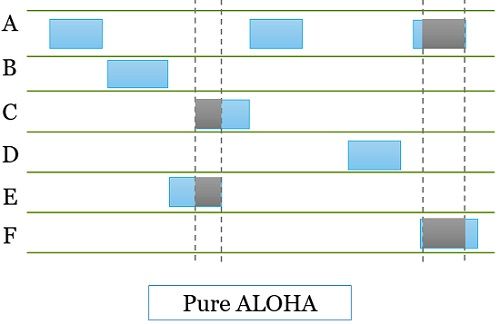
Thus, in pure ALOHA protocol, every station sharking the same link waits for a random amount of time before resending the frame to avoid the collision.
- The vulnerable time (the length of time in which there is a possibility of collision) for pure ALOHA is:
Vulnerable Time = 2 × Tfr
Where Tfr is the frame transmission time. - The Average number of successful transmissions for pure ALOHA is:
S = G x e-2G
Where G is the average number of frames generated by the system during one frame transmission time. - Maximum throughput Smax is when G = 1/2, i.e. 0.184.
Slotted ALOHA
Slotted ALOHA was developed to resolve the issues with pure ALOHA. The slotted ALOHA divides the time into slots, and each station is asked to send a frame only at the beginning of the new slot.
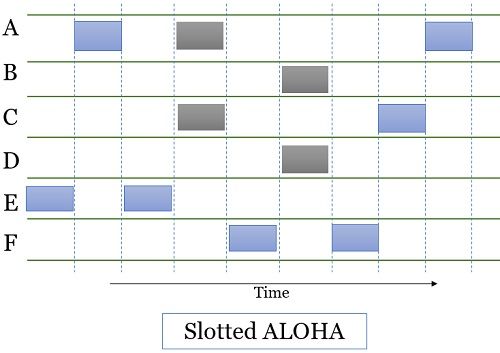
However, there is still the possibility of collision as two or more stations may send frames at the beginning of the same time slot.
- Vulnerable Time = Tfr
Where Tfr is the frame transmission time. - Successful Transmissions for slotted ALOHA is:
S = G x e-G
where G is the average number of frames generated by the system during one frame transmission time - Maximum throughput Smax is:
when G = 1, i.e. 0.368.
Carrier Sense Multiple Access (CSMA)
In the carrier sense multiple access method, the stations would initially sense the shared link before transmitting the frame. It works on the principle of “sense before you transmit”.
However, the CSMA only reduces the chances of collision. It does not completely eliminate it. The reason for the collision is propagation delay. Whenever a station sends a frame to another station, it takes time for the first bit to reach the destination station and for the station to sense it.
It may happen that the destination station senses the channel and finds it idle. As the first bit sent from the sender is yet not received. Thus, the destination station also starts sending the frame to other stations.
So, the frame from sender to destination and from destination to other station will collide and will get destroyed.
Vulnerable Time = Tp
Where Tp is the time required by frame to travel from one end of the medium to the other end.
However, to avoid this collision, the CSMA has introduced some access methods. We refer to these methods as persistence methods. The persistence methods will help the station share the same medium in answering the questions like:
- What should a station do if it finds the channel idle?
- What should a station do if it finds the channel busy?
Persistence Methods
- I-Persistent Method
- Non-Persistent Method
- p-Persistent Method
I-Persistent Method
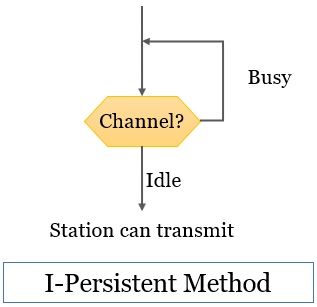
A station senses the channel continuously, and as soon as it finds it idle, it sends the frame. Although the method has the highest chance of collision.
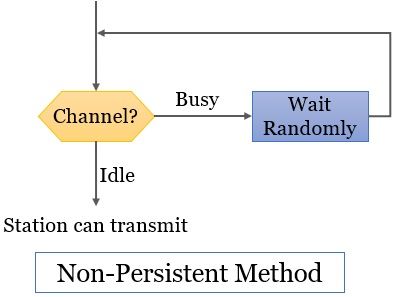
Non-Persistent Method
The station senses the channel, and if it finds itself busy, it waits for a random amount of time and rechecks the channel again. The check is performed until it finds the channel idle. As soon as the station senses that the channel is idle, it sends the frame. The method reduces the efficiency of the network as it may happen that the channel remains idle where stations are still trying to send frames.
p-Persistent Method
The network uses the p-persistent method when the time is divided into slots. The duration of each time slot must be equal to or greater than the maximum propagation time. Here, when the station senses the channel and finds it idle, it has to follow these steps:
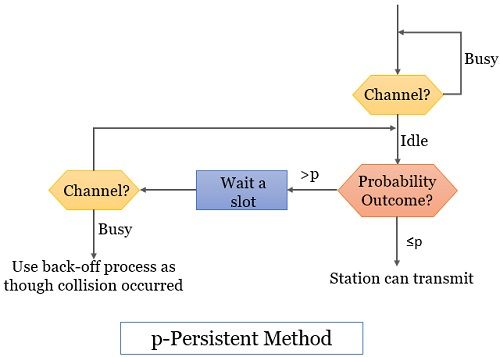
- The station transmits the frame with probability p.
- Then, the station waits for the beginning of the next time slot with the probability of q = 1 – p. As the next time slot begins, the station rechecks.
- If the station finds the channel idle, it performs step 1.
- If the channel is busy, the station uses a back-off process though the collision has occurred.
Carrier Sense Multiple Access with Collision Detection (CSMA/CD)
The CSMA method does not define what a station must do if a collision occurs. CSMA/CD protocol provides a way to handle the collision. The station senses the channel, and if it finds it idle, it sends the frame. After sending the frame, the station keeps on monitoring the channel to see if any collision occurs.
If no collision occurs, it means the transmission was successful. And if the collision has occurred, the station sends a jamming signal on the network notifying other stations about the collision. The station then waits for a random amount of time and resends the frame.
Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA)
The CSMA/CA protocol is used for wireless networks. In a wireless network, the stations cannot sense any collisions on the network as there is no physical medium (cable). So, instead of detecting the collision, the protocol focuses on avoiding the collision.
To avoid a collision, the CSMA/CA protocol works with three strategies:
Interframe Space (IFS)
The station keeps on sensing the channel continuously, and as it finds it idle, it does transmit immediately. This waiting time is referred to as IFS. The IFS is different for each station. The IFS is also used to prioritize the stations like stations with small IFS have the highest priority.
Contention Window
The contention window is a time slot after IFS. This time slot is divided into several mini-slots. After waiting for the IFS time, the station then again waits for the random amount of mini-slots of contention windows.
Now how does the station decide for what random amount of minislots it has to wait?
Well, the station decides the number of mini-slots according to the binary exponential back-off strategy. It means after IFS waiting, the station waits in the contention window for one mini-slot. Then the station checks the channel; if found idle, then it transmits. Else if it finds it busy, the number of mini-slots will double each time after IFS.
For example, after IFS, this time, the station has to wait for four mini-slots.
Then after the end of each mini-slot, it checks. Now, after 1st mini-slot, it senses the channel idle, so it will continue waiting for 2nd mini-slot, again idle, and continue waiting for 3rd mini-slot; now it finds the channel busy, and the timer of the contention window stops.
The timer starts when the channel becomes idle and lets the station finish the 4th mini-slot. After completing waiting for the 4th mini-slot station, checks the channel; if idle, send data. If busy again, starts with IFS.
Acknowledgement
The contention window is not the last. After sending the data, the station then again waits for a particular interval for acknowledgement. If the acknowledgement is received before the timeout, the transmission is successful. Else, resend the data.
Controlled Access Protocol
In the controlled access protocol, the stations in the network consult each other station to identify if any of the stations have control over the channel. So, a station is not allowed to transmit until it has been authorized to transmit, which eliminates the chances of collision. So, there are control access methods to authorize the stations for transmitting.
Reservation
In the reservation method, every station in the network has to make a reservation if it is interested in transmission. The time is divided into slots. In each time slot, the reservation frame precedes the frames that are transmitted in that slot.
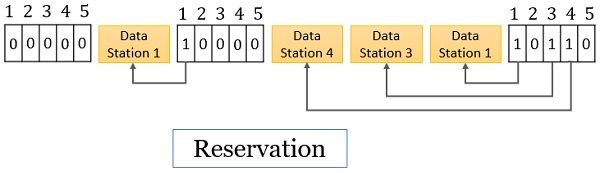
The reservation frame is also divided into N number of mini-slots, where N is the number of stations in the network. Each mini slot in the reservation frame belongs to a particular station. So, stations who are interested in transmission make the reservation in their associated mini slots.
So only those stations send frames along with the reservation frame that has made reservations.
Polling
With the polling strategy, one station in the network is designated as the primary station. The rest of the stations are referred to as secondary stations. Now whenever the station has to communicate with the other station in the network, the communication has to be made through the primary network.
Thus, the primary station decides which station will use the channel. When the primary station wants to send data, it asks the corresponding secondary station whether it is ready to receive or not via the select function. If the primary station wants to receive data, it asks the secondary stations whether they have something to send via the poll function.
So only the primary station initiates the communication and has full control over the link. No secondary station can initiate communication on its own.
Select Function
Consider that the primary station is ready to send data, and it knows that the link is available. What it has to check is whether the particular secondary station is ready to receive the data. So, it alerts the secondary station by sending a select frame.
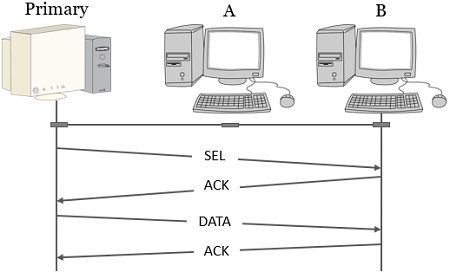 Now, if the secondary station responds with a positive acknowledgement, it is considered that the station is ready to accept data. So, the primary stations send data to which again the secondary station responds with positive acknowledgement if the transmission was successful.
Now, if the secondary station responds with a positive acknowledgement, it is considered that the station is ready to accept data. So, the primary stations send data to which again the secondary station responds with positive acknowledgement if the transmission was successful.
Poll Function
When the primary station wants to receive data, it polls each of the secondary stations one at a time. If the secondary station has data to send, it responds to the poll with the data frame, which the primary station later acknowledges if the transmission was successful.
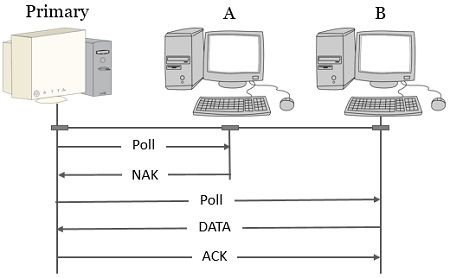
In case the polled secondary station has nothing to send, it will simply respond with a negative acknowledgement.
Token Passing
In the token passing, all the stations in the network are arranged in a logical ring such that each station has a predecessor and a successor. In this strategy, a special packet referred to as a token is passed from one station to another station. Only the station currently holding the token has control over the channel and is allowed to transmit.

After an interval, the station has to pass this token to the successor station. Once the successor station receives the token, it gets control over the channel. If the station receiving the token doesn’t have any data to transmit, it simply passes the token to its successor station. And the cycle goes on.
only one station possessing the token has control over the channel at a time. No other station can transmit other than the station holding the token.
Channelization
Channelization allows multiple stations in a network to access the channel by dividing the available bandwidth on the basis of frequency, time and code.
Frequency Division Multiple Access (FDMA)
In the frequency division multiple access methods, the bandwidth of the channel is divided into multiple frequency bands. Each station in the network is assigned a separate frequency band, and this frequency band is available to the station all the time.
So, whenever a station has data to send, it sends simply sends the data on the assigned frequency band.
Time Division Multiple Access (TDMA)
In the time division multiple access methods, the available bandwidth of the channel is divided on the basis of time. Each station is allotted a specific time slot, and only in this time slot is the station able to transmit.
For example, in schools or colleges, the available duration is divided on the basis of time. A particular time slot is allotted to each subject teacher, and only in this time slot, the teacher can deliver his or her lecture. As the time slot ends, the other subject teacher gets a chance to deliver the lecture.
Code Division Multiple Access (CDMA)
The code division multiple access methods allow all the stations to transmit data simultaneously. Of course, there is a chance of collision in this scenario. To avoid a collision, the two-communicating stations are assigned a distinct code. The particular code is only inferred by the stations to which it is assigned; the rest of the stations cannot infer this code.
For example, in a room, there are many people. Now, if all the communicating pairs will speak in the same language, none is going to understand anything. But if each pair will communicate in a different language which is only known to them, then communication between several pairs is possible in a single room at the same time. The strategy is communication with different codes.
This is all about the multiple access protocols. So far, we have discussed three types of multiple access protocols, i.e. random access, controlled access, and multiple access. We have also explored types of these three kinds of protocol.

Leave a Reply