Block cipher is an encryption and decryption method which operates on the blocks of plain text, instead of operating on each bit of plain text separately. Each block is of equal size and has fixed no of bits. The generated ciphertext has blocks equal to the number of blocks in plaintext and also has the same number of bits in each block as of plain text. Block cipher uses the same key for encryption and decryption.
In this section, we will discuss the definition of block cipher. We will also consider the design principle of a block cipher and the modes of operation of the block cipher.
Content: Block Cipher in Cryptography
What is Block Cipher
Block cipher is an encryption method which divides the plain text into blocks of fixed size. Each block has an equal number of bits. At a time, block cipher operates only on one block of plain text and applies key on it to produce the corresponding block of ciphertext.
While decryption also only one block of ciphertext is operated to produce its corresponding plain text. Data Encryption Standard (DES) is the best example of it.
DES divides the plain text into the number of blocks, each of 64-bit. DES operates on one block of plain text at a time. Key of 56-bit is applied to each block of plain text to produce its corresponding ciphertext of 64-bit.
During decryption also only one block of ciphertext is operated at a time to produce its corresponding block plain text. In DES the decryption algorithm is the same as the encryption one.
On an all the block cipher operates on a block of bits at a time instead of one bit a time. Operating bit by bit is a very time-consuming process and as block cipher is a computer-based cryptographic algorithm it needs to be fast. That’s why operating one block of bits at a time makes it faster as compared to a stream cipher.
But there was a limitation in the block cipher as it would generate the same ciphertext for the repeating text pattern in plain text. However, this limitation was resolved by implementing chaining in the block cipher.
Block Cipher Principles
A block cipher is designed by considering its three critical aspects which are listed as below:
- Number of Rounds
- Design of Function F
- Key Schedule Algorithm
1. Number of Rounds
The number of rounds judges the strength of the block cipher algorithm. It is considered that more is the number of rounds, difficult is for cryptanalysis to break the algorithm.
It is considered that even if the function F is relatively weak, the number of rounds would make the algorithm tough to break.
2. Design of Function F
The function F of the block cipher must be designed such that it must be impossible for any cryptanalysis to unscramble the substitution. The criterion that strengthens the function F is it non-linearity.
More the function F is nonlinear, more it would be difficult to crack it. Well, while designing the function F it should be confirmed that it has a good avalanche property which states that a change in one-bit of input must reflect the change in many bits of output.
The Function F should be designed such that it possesses a bit independence criterion which states that the output bits must change independently if there is any change in the input bit.
3. Key Schedule Algorithm
It is suggested that the key schedule should confirm the strict avalanche effect and bit independence criterion.
Block Cipher Modes of Operation
There are five important block cipher modes of operation defined by NIST. These five modes of operation enhance the algorithm so that it can be adapted by a wide range of applications which uses block cipher for encryption.
- Electronic Code Book Mode
- Cipher Block Chaining Mode
- Cipher Feedback Mode
- Output Feedback Mode
- Counter Mode
1. Electronic Feedback Mode
This is considered to be the easiest block cipher mode of operation. In electronic codebook mode (ECB) the plain text is divided into the blocks, each of 64-bit. Each block is encrypted one at a time to produce the cipher block. The same key is used to encrypt each block.
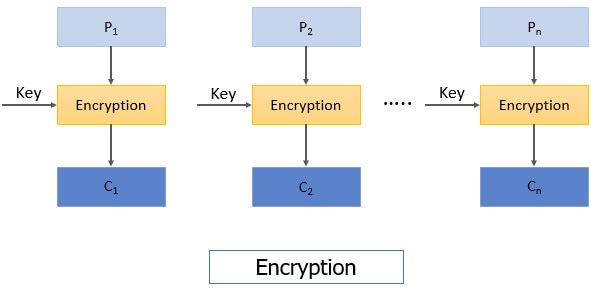
When the receiver receives the message i.e. ciphertext. This ciphertext is again divided into blocks, each of 64-bit and each block is decrypted independently one at a time to obtain the corresponding plain text block. Here also the same key is used to decrypt each block which was used to encrypt each block.
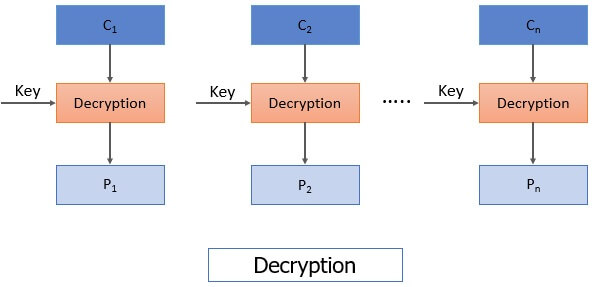
As the same key used to encrypt each block of plain text there arises an issue that for a repeating plain text block it would generate the same cipher and will ease the cryptanalysis to crack the algorithm. Hence, ECB is considered for encrypting the small messages which have a rare possibility of repeating text.
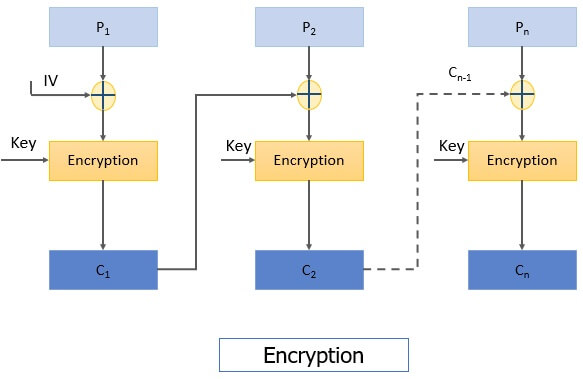
2. Cipher Block Chaining Mode
To overcome the limitation of ECB i.e. the repeating block in plain text produces the same ciphertext, a new technique was required which is Cipher Block Chaining (CBC) Mode. CBC confirms that even if the plain text has repeating blocks its encryption won’t produce same cipher block.
To achieve totally different cipher blocks for two same plain text blocks chaining has been added to the block cipher. For this, the result obtained from the encryption of the first plain text block is fed to the encryption of the next plaintext box.
In this way, each ciphertext block obtained is dependent on its corresponding current plain text block input and all the previous plain text blocks. But during the encryption of first plain text block, no previous plain text block is available so a random block of text is generated called Initialization vector.
Now let’s discuss the encryption steps of CBC
Step 1: The initialization vector and first plain text block are XORed and the result of XOR is then encrypted using the key to obtain the first ciphertext block.
Step 2: The first ciphertext block is fed to the encryption of the second plain text block. For the encryption of second plain text block, first ciphertext block and second plain text block is XORed and the result of XOR is encrypted using the same key in step 1 to obtain the second ciphertext block.
Similarly, the result of encryption of second plain text block i.e. the second ciphertext block is fed to the encryption of third plain text block to obtain third ciphertext block. And the process continues to obtain all the ciphertext blocks.
You can see the steps of CBC in the figure below:
Decryption steps of CBC:
Step 1: The first ciphertext block is decrypted using the same key that was used for encrypting all plain text blocks. The result of decryption is then XORed with the initialization vector (IV) to obtain the first plain text block.
Step 2: The second ciphertext block is decrypted and the result of decryption is XORed with the first ciphertext block to obtain the second plain text block. And the process continues till all plain text blocks are retrieved.
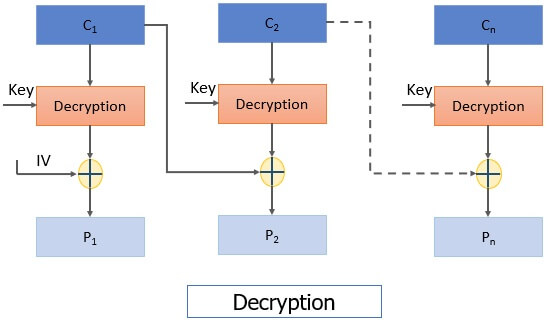
There was a limitation in CBC that if we have two identical messages and if we use the same IV for both the identical message it would generate the same ciphertext block.
3. Cipher Feedback Mode
All applications may not be designed to operate on the blocks of data, some may be character or bit-oriented. Cipher feedback mode is used to operate on smaller units than blocks.
Let us discuss the encryption steps in cipher feedback mode:
Step 1: Here also we use initialization vector, IV is kept in the shift register and it is encrypted using the key.
Step 2: The left most s bits of the encrypted IV is then XORed with the first fragment of the plain text of s bits. It produces the first ciphertext C1 of s bits.
Step 3: Now the shift register containing initialization vector performs left shift by s bits and s bits C1 replaces the rightmost s bits of the initialization vector.
Then again, the encryption is performed on IV and the leftmost s bit of encrypted IV is XORed with the second fragment of plain text to obtain s bit ciphertext C2.
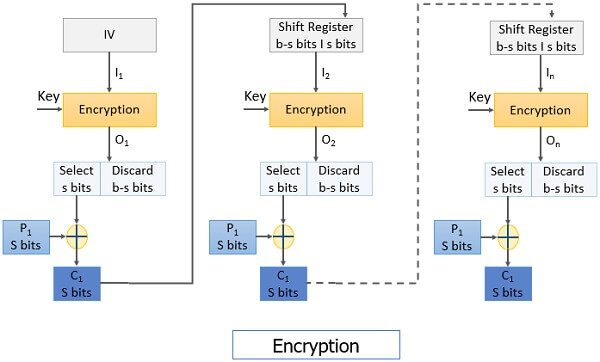
The process continues to obtain all ciphertext fragments.
Decryption Steps:
Step 1: The initialization vector is placed in the shift register. It is encrypted using the same key.
Keep a note that even in the decryption process the encryption algorithm is implemented instead of the decryption algorithm.
Then from the encrypted IV s bits are XORed with the s bits ciphertext C1 to retrieve s bits plain text P1.
Step 2: The IV in the shift register is left-shifted by s bits and the s bits C1 replaces the rightmost s bits of IV.
The process continues until all plain text fragments are retrieved.
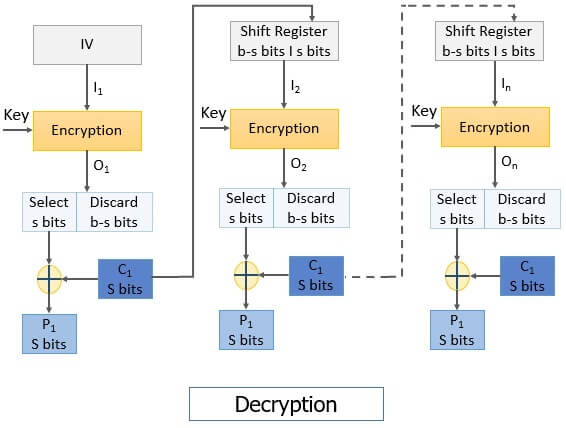
It has a limitation that if there occur a bit error in any ciphertext Ci it would affect all the subsequent ciphertext units as Ci is fed to the encryption of next Pi+1 to obtain Ci+1. In this way, bit error would propagate.
4. Output Feedback Mode
The output feedback (OFB) mode is almost similar to the CFB. The difference between CFB and OFB is that unlike CFB, in OFB the encrypted IV is fed to the encryption of next plain text block. The other difference is that CFB operates on a stream of bits whereas OFB operates on the block of bits.
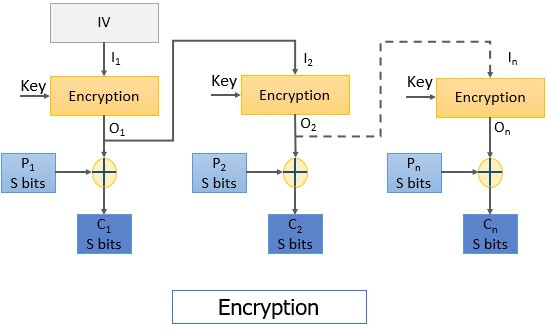
Steps for encryption:
Step 1: The initialization vector is encrypted using the key.
Step 2: The encrypted IV is then XORed with the plain text block to obtain the ciphertext block.
The encrypted IV is fed to the encryption of next plain text block as you can see in the image below.
Steps for decryption:
Step 1: The initialization vector is encrypted using the same key used for encrypting all plain text blocks.
Note: In the decryption process also the encryption function is implemented.
Step2: The encrypted IV is then XORed with the ciphertext block to retrieve the plain text block.
The encrypted IV is also fed to the decryption process of the next ciphertext block.
The process continues until all the plain text blocks are retrieved.
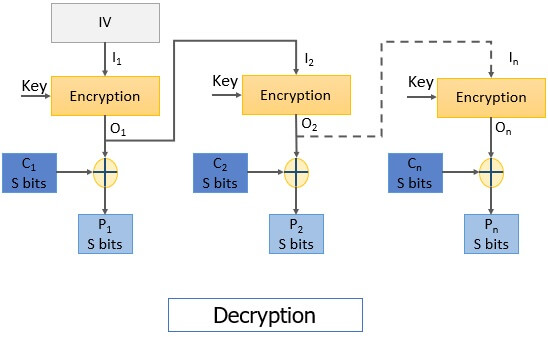
The advantage of OFB is that it protects the propagation of bit error means the if there occurs a bit error in C1 it will only affect the retrieval of P1 and won’t affect the retrieval of subsequent plain text blocks.
5. Counter Mode
It is similar to OFB but there is no feedback mechanism in counter mode. Nothing is being fed from the previous step to the next step instead it uses a sequence of number which is termed as a counter which is input to the encryption function along with the key. After a plain text block is encrypted the counter value increments by 1.
Steps of encryption:
Step1: The counter value is encrypted using a key.
Step 2: The encrypted counter value is XORed with the plain text block to obtain a ciphertext block.
To encrypt the next subsequent plain text block the counter value is incremented by 1 and step 1 and 2 are repeated to obtain the corresponding ciphertext.
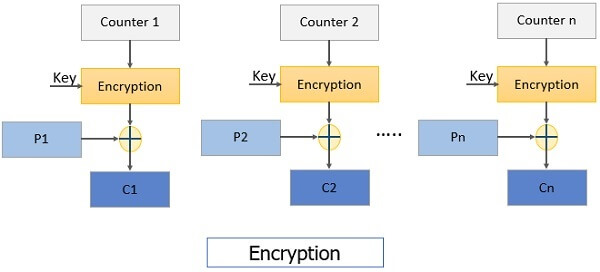
The process continues until all plain text block is encrypted.
Steps for decryption:
Step1: The counter value is encrypted using a key.
Note: Encryption function is used in the decryption process. The same counter values are used for decryption as used while encryption.
Step 2: The encrypted counter value is XORed with the ciphertext block to obtain a plain text block.
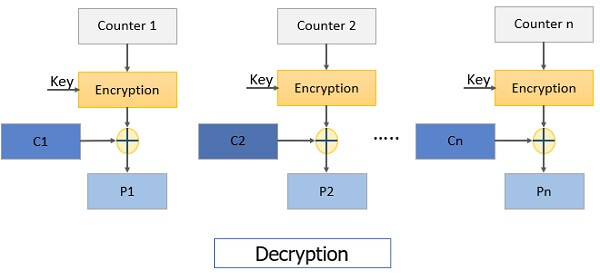
To decrypt the next subsequent ciphertext block the counter value is incremented by 1 and step 1 and 2 are repeated to obtain corresponding plain text.
The process continues until all ciphertext block is decrypted.
So, this is all about Block cipher, its designing principles and its mode of operation.

Amirul Islam says
Hello,
I am in trouble to understand and need the right answers and solutions with proper elaborate explanation of the following questions.
01. For CBC, what would be the encryption for 0010 1111 1001 0100 1100 with IV 1101 with key 0110?
02. For CBC, what would be the decryption for 1101 0101 0110 0001 0110 with IV 1011?
I hope some of you must reply of my questions.
Kind Regards
Amirul Islam
Farhan Khan says
Cleared My Doubt. Thanks