Data Encryption Standard (DES) is the symmetric block cipher which encrypts a 64-bit plain text in a 64-bit ciphertext. The DES was introduced by the National Institute of Standard and Technology (NIST) in the 1970s. Initially, DES was only used in financial applications but later it was accepted as the cryptographic algorithm by other organizations too.
Being a symmetric cipher the same key is used in encryption and decryption process of DES. In this context, we will discuss the steps performed in DES and we will also discuss the advantages and disadvantages of DES.
Content: Data Encryption Standard (DES)
DES Definition
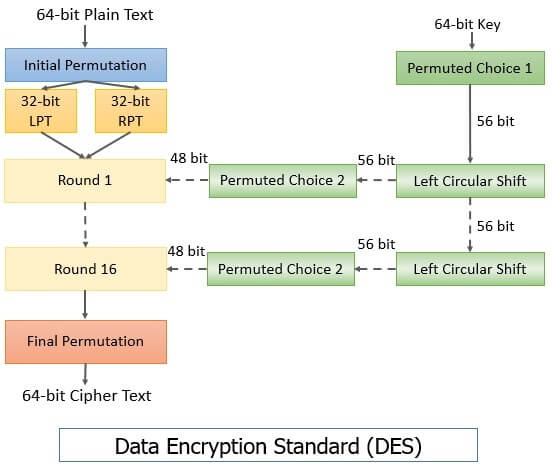
Data Encryption Standard is a symmetric block cipher which takes the input of 64-bit plain text along with 64-bit key and process it, to generate the 64-bit ciphertext. The diagram below illustrates the working of DES. We will discuss its step in brief.
Encryption
Step 1: In the first step the 64-bit plain text undergoes initial permutation which rearranges the bits to produce two 32-bit permuted block which is called left plain text (LPT 32-bit) and right plain text (RPT 32-bit).
Step 2: Now, 16 rounds of DES encryption will be performed on this LPT and RPT with a 56-bit key.
Step 3: After the 16th round the 32-bit LPT and 32-bit RPT are integrated which forms a 64-bit block again and then the final permutation is applied to this 64-bit block, to obtain the 64-bit ciphertext.
Decryption
The same Data Encryption Standard algorithm used for encrypting the plain text is also used to decrypting the ciphertext. But the algorithm is reversed, such as the initial and final permutation events are reversed. Even the sequence of the subkeys applied in 16 rounds of DES are also reversed.
Rounds in Data Encryption Standard
Now, we will discuss the process that takes place during the 16 rounds of DES algorithm. Each round of DES performs the same function. So, below are the steps of the function performed in each round of DES algorithm:
- Key Transformation
- Expansion Permutation
- S-box Substitution
- P-box Permutation
- XOR and Swap
1. Key Transformation
Earlier we have discussed that the initial key size is 64-bit which is reduced to the 56-bit key. This is done by discarding every 8th bit from the 64-bit key. So, for each round of DES, this 56-bit key is used. In the key transformation step, this 56-bit is transformed to the 48-bit key. Let’s see how?
The 56-bit key is split into two halves. Each half is of 28-bit. Now, a left circular shift is implemented on both the halves which shift the bits in two halves by one or two positions depending on the order of the round.
If the round number is 1, 2, 9, 16 then the left circular shift is done by one position else, if any other order number is encountered the circular shift is done by two positions.
After the left circular shift both the 28-bit halves are integrated and permutation is performed on a 56-bit key. And from this permuted 56-bit key 48-bit subkey is selected. As the key transformation step involves permutation along with compression of the 56-bit key to 48-bit subkey it is also called compression permutation.
Thus, the key transformation step provides a different 48-bit subkey for each round of DES.
2. Expansion Permutation
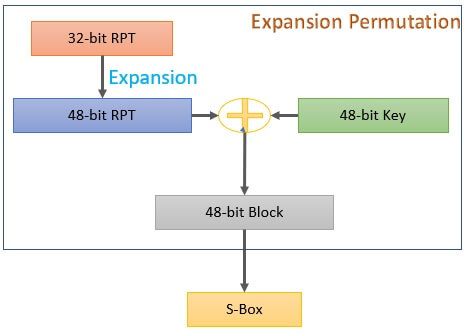
In the first step of encryption, during the initial permutation of DES, the 64-bit plain text is permuted and we have 32-bit LPT and 32-bit RPT. Now, the expansion permutation is performed on the 32-bit RPT which transforms it from 32-bit to 48-bit. The 32-bit LPT is untouched during the process.
For expansion, the 32-bit RPT is divided 8 blocks, where each block is of 4-bit. Each block of 4-bit is expanded to block of 6-bit as you can see in the image below. The extreme two bits of the block are repeated and the middle two-bits is passed on as it is.
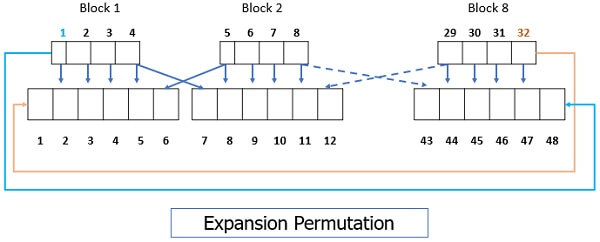
After expansion, now the 48-bit RPT is XORed with the 48-bit key and the resultant 48-bit block is transferred to S-box substitution.
3. S-box Substitution
The input to S-box is 48-bit resultant block of expansion permutation. In S-box substitution, the input 48-bit block is transformed to 32-bit block but the question is how?
The 48-bit input block to S-box substitution is divided into 8 blocks of 6-bit each and is provided as input to 8 substitution boxes also called S-boxes. Each s-box has an input of 6-bit and its outputs 4-bit.
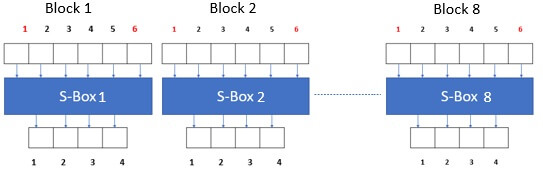
Each S-box is considered as the table which has 4 rows 0-3 and 16 columns i.e. 0-15. Why 4 rows and 16 columns? Because from the 6-bit input to s-box the two extreme bits are used to determine the number of rows.
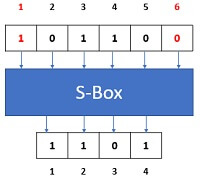
2 bits can form 4 combinations of 0s and 1s:
22 = 4 rows
The middle 4 bits are used to determine the number of columns
42 = 16 columns
Now, we will see how the 6-bit input is transformed to the 4-bit output. For example, in the figure above you can see that input bit, at position 1 and 6 i.e. ‘10’ that represent 2 which determines 2nd row and middle 4 bits i.e. ‘0110’ that represent 6 which determines the 6th column of s-box. The value at the intersection of the 2nd row and 6th column will represent the 4-bit output of corresponding s-box.
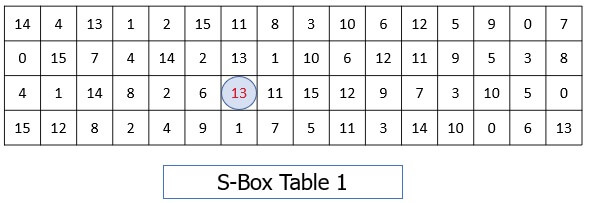
In our example, the intersection of the 2nd row and 6th column is 13 its 4bit representation is 1101. So, the output of S-box 1 is 1101.
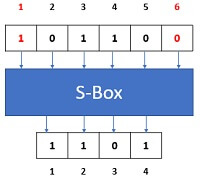
Similarly, the remaining S-boxes function will be carried out to find the remaining 4-bit outputs. In this way, the 8 s-boxes would generate 8, 4-bit output blocks which when integrated forms 32-bit output.
4. P-box Permutation
The 32-bit output obtained from s-box substitution is provided as an input to P-box. Here, the 32-bit input is simply permuted and send to the next step.
5. XOR and Swap
As you can observe so far, we have been operating on the 32-bit RPT of the initial 64-bit plain text. The 32-bit LPT is still untouched. In this step, the 32-bit LPT of the initial 64-bit plain text is XOR with the output of P-box permutation.
The result of the XOR is the new RPT for next round and the old RPT is swapped with LPT. S So, the old RPT is now new LPT for next round. o, the old RPT is now new LPT for next round.
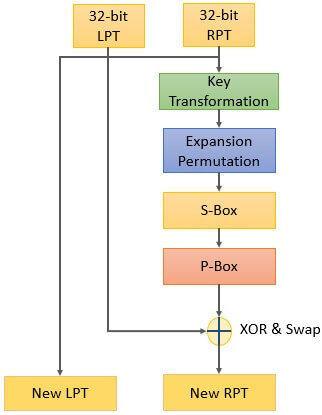
So, here the process of a single round ends and next round start which has the same function.
After 16 such rounds, the output of the 16th round undergoes final permutation. The result of this final permutation is 64-bit ciphertext.
Advantages and Disadvantages of DES
- DES has a 56-bit key which raises the possibility of 256 possible keys which make brute force impossible.
- The 8 S-boxes used in each round were not made public and even it impossible for any to discover the design of the s-boxes which makes the attack more impossible.
- The number of rounds in DES increases the complexity of the algorithm.
- However, the cryptanalysis attack is easier than the brute force attack on DES.
Key Takeaways
- DES is a symmetric block cipher.
- DES encrypts 64-bit plain text to 64-bit cipher text.
- DES uses a 56-bit key for encryption.
- Encryption and decryption algorithm is the same in DES. But, the procedure of encryption is reversed while decryption.
- 16 rounds in DES strengthens the algorithm.
- Each round has the same function which involves key transformation, expansion permutation, s-box substitution, p-box permutation and XOR and swapping.
So, this is all about the DES block cipher. In 2001 the NIST has published Advanced Encryption Standard (AES) to replace DES. Because DES was meant for the hardware and its relatively slow performance on software leads to its replacement.

Dominic Sheppard says
Do you have any more information on binary encryptions?
Mohamed Abdul Kader says
Very Concise and Nice Material.
Thanks a Lot.